By: Evgeniya Vi.
17 MAY 2018
4182
How can you protect the idea for a mobile application and the final product from copying and theft? Is it important? Undoubtedly. You can’t even imagine how many people are left with nothing because they didn’t give due attention to the issue of security for their ideas and how many brilliant ideas simply perish due to ignorance of appropriate safeguards. At first glance, an idea is nothing. The idea is not a product, a ready technology, a ready concept, and not a service. While you may think your idea is not interesting to anyone but you, your idea can easily be stolen. The stolen idea may turn into a product faster than you think, and your potential users and revenue will simply slip away from you.
Protecting your idea is much more difficult than protecting the finished product because it is very difficult to prove that an idea belongs to you. Stealing an idea is like a disease that is easier to prevent than cure. Only preventive measures will help you save your idea and, if necessary, prove that the product belongs to you.
When to start? is the wrong question. The correct question is, How can I protect my project at different stages of its development?
It's very simple:
- First, an idea is born.
- Then, the idea is embodied in the product.
- Finally, the product is developed and realized.
Protecting your startup from theft can occur at each stage in different ways, so you can’t ignore any of them.
How to protect your startup idea from being stolen
You have a brilliant idea that you plan to implement. Right now, it seems to you that it’s interesting only to you. Really, who needs your thoughts and your research? Since it’s just an idea and not developed in real life, it can’t possibly interest anyone, right? Making such judgments is the most common mistake.
Your idea is the most valuable thing that you have at the start, so you need to have a thought-out strategy for its implementation that takes into account how to reliably protect your idea.
In order to implement the project, you will have to share information. This is not relevant when you have enough technical knowledge and skills to develop your idea into a finished product on your own. However, more often than not, you will need to disclose your idea to others in order to create a minimum viable product (MVP) and a prototype, write detailed technical documentation for the project, and more. The product concept, a unique algorithm, or technology are also under the threat of copying and theft.
Thus, the most effective preventive measure against the copying and theft of your idea is a careful choice of partners, providers, and consultants. Use popular platforms and resources, such as Clutch or GoodFirms, to collect and analyze information about potential providers and partners.
Even if you are completely confident in the people with whom you are ready to discuss your idea, you should never fully disclose your idea. Before you document your intentions, dialogue should be conducted without details. Pay attention to technologies, implementation issues, and other technical issues that will give you the opportunity to gather the necessary information for the implementation of the project but won’t necessarily give third parties the opportunity to fully understand the concept of your future product.
In addition, it is extremely important to sign a document that legally protects your idea and your product and limits third parties. Such a document is called a non-disclosure agreement (NDA). We will talk about these a little later because it is part of the implementation of your idea and, as a rule, is signed in parallel with the contract on software development. However, you’re not limited to requiring the signing of this document before the assessment and development process begins. If the provider suggests that you sign an NDA even before you start discussing your idea, this is an additional sign for you that this provider can be trusted.
You can often find information arguing that it is appropriate to patent the idea at this stage. This is a controversial issue because:
- You will spend a lot of time doing this, and it is more expedient to invest in the implementation of the idea
- You will spend the money that you need to invest in development
- During development, your idea, concept, or technology can be transformed, improved, or changed; and it may eventually turn out that you have not patented the product that was originally envisioned.
Alternatively, you can apply for a preliminary patent. This will give you one year to study your idea and understand how unique and profitable it is.
How to protect your project from being copied at the development stage
This stage assumes that you provide complete information about your future product to your partners. This is the stage where your idea gets technical characteristics, which are set out in the documentation for the project.
Even if you have taken into account the issue of security at the project idea stage and trust your partners, it is extremely important for you to document your confidence through some legally binding means, if it was not done earlier.
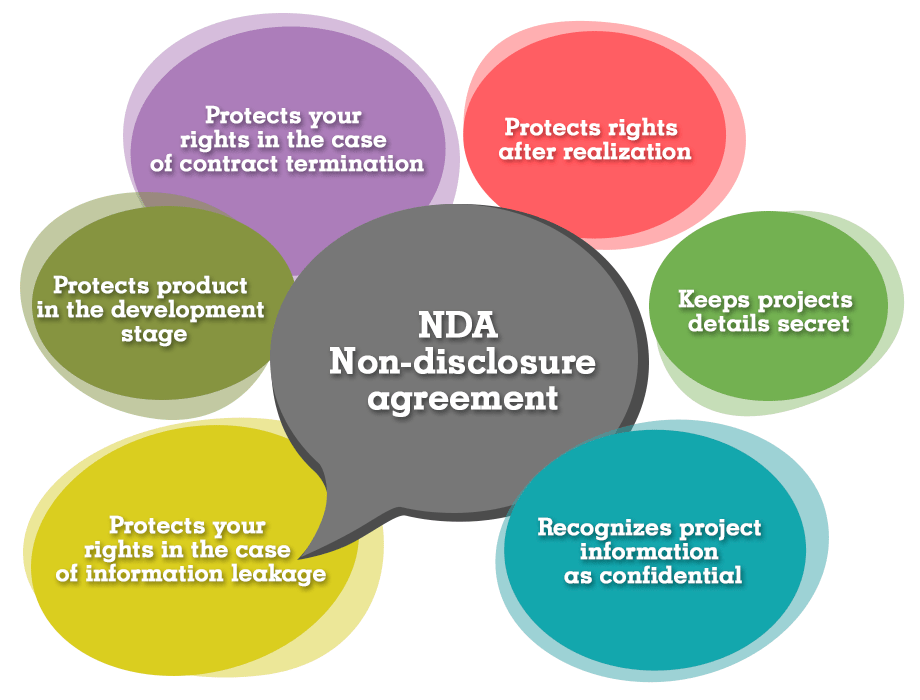
The security of your project at this stage can be documented by a non-disclosure agreement (NDA).
What is an NDA and why is this document important?
An NDA agreement is an agreement on trade secrets. Parties to this contract are the client/customer, who is the owner of the product, and the mobile app development company.
According to the NDA, the development company (executor) must keep the following information secret:
- Data about the client and his business/product
- The idea of a project that gives the client an advantage in the market
- Software source codes
- Trial software versions
- Design of the project
- Formulas and algorithms used in software
- Technical documentation, etc.
If the contractor violates the NDA, the customer is entitled to apply to the court and prove the theft of the information. In this case, the contractor will pay the customer the penalties approved in the NDA.
In turn, the software company must take measures to prevent its employees from transferring confidential information to third parties. If this occurs, the developer will bear serious financial responsibility for the breach.
The term of an NDA is usually up to 5 years. It is generally accepted that beyond that point, information becomes obsolete and no longer requires confidentiality.
Appus Studio provides the following form of NDA |
|---|
It is extremely reckless to start working without signing an NDA. For you, an NDA is:
- Recognition that the project is confidential
- Protection of your rights in case of information leakage
- A guarantee of maintaining your rights to the product after the release and/or in the case of contract termination
- Protection of your product and its components at the development stage and after the release
Before signing an NDA, carefully read the document and make sure that it really can provide you with adequate protection and guarantees. The NDA must contain not only a list of obligations but also information on remedies in the case of breach of contract and information regarding under which jurisdiction the disputable issues will be resolved.
How to protect your mobile app from being cloned and copied after launching
At this stage, your product is most vulnerable because it is open and accessible to the audience. On the other hand, it is also at this stage that you can most effectively protect your project. Not so long ago, app stores began to struggle with app clones and copies. Let's recall the situation with the game Flappy Bird. It was cloned so completely that, according to the research of The Guardian portal, a third of all games published in the Appstore in one day were clones of Flappy Bird. There are many examples of this. Such situations were, are, and will be caused by a simple fact: product ideas require inspiration. However, there is a very fine line between using another’s product as inspiration and copying or cloning it, so it is very important to have powerful safeguards in place to prove your right to the product and win back your users from clones and copies.
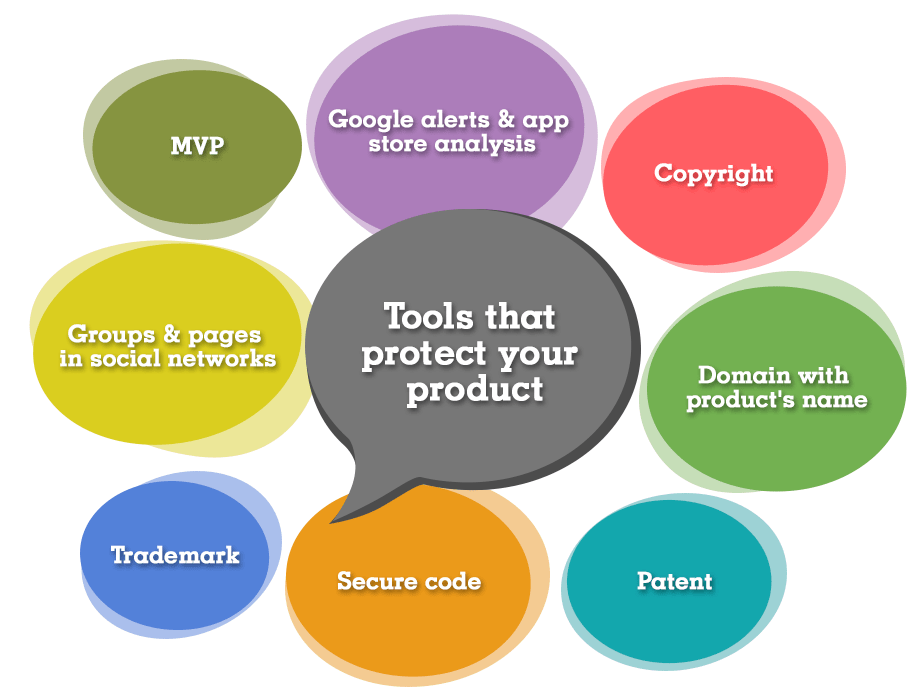
Here are some effective direct and indirect safeguards that will help you easily prove that the idea, concept, technology, design, and other components belong to you:
Trademark |
This is an effective way to protect your product from cloning and copying, but it is a rather complicated approach. Register the name of the trademark for all functions and services implemented in the application. Badges, symbols, logos, slogans, phrases, and other elements associated with your application will limit your competitors and help you legally protect your ownership of the product. A trademark may be used at the design stage. Once you have received the finished design of your product, you can safely apply for the registration of the trademark. |
|---|---|
Patent |
This is a stronger legal way to protect your rights to a product than a trademark. However, its design is more laborious and expensive. You can start with a pre-patent, which is issued for one year and provides some protection. |
MVP |
As previously noted, the start of the project should ideally begin with the release of the minimum viable product. In addition to being effective from the point of view of implementing a successful project, it also provides protection for your idea and project. Once an MVP is published and publicly available, your idea is protected by copyright as the first published. Just like books, applications are protected by copyright law. Additionally, you will get an advantage in the market. |
Copyright |
In addition, you should write about your copyright in your application. A copyright notice will significantly reduce your competitors' attempts to use your product for copying or cloning. |
Secure code |
Do not spare investment in development. Professional and highly skilled specialists will cost you more, but you will get a product with a thoughtful architecture that cannot be hacked and from which code cannot be copied. |
Domain with product name |
A good name has a strong effect, and buying your domain at an earlier time than a competitor's registered trademark can solve many issues when it comes to resolving any disputes. |
Groups and/or pages with the name and symbol of the project in social networks |
As with the domain, good names also achieve good search positions, are well remembered, and become unavailable to competitors. |
Google alerts |
Set up notifications for the keywords and the name of your project so you will know when to exit similar applications and react in a timely manner to copies or clones of your product. |
App stores analysis |
Do not be too lazy to monitor new items in app stores. There is a possibility that you will stumble upon a clone or a copy of your product and can begin to take action. |
In conclusion
The best ways to protect your idea and your product from being stolen, cloned, and copied are:
- Take care of all information about your project.
- Choose reliable partners.
- Use legal instruments at all stages of the start-up (NDA, trademark, patent, etc.).
- Use additional tools to prevent cloning and copying (domains, alerts, social networks, copyright, etc.).
- Invest in security.
If you find that your idea, the concept, the unique functions of your product, etc. have been stolen, this is something to celebrate. It is a great indicator that your idea and your product are unique, worthwhile, and potentially successful! Don’t despair. Simply try to prove your authorship and ownership.
Here are some tips to get justice:
- Contact the clone owners directly with a request to stop using and promoting the clone of your application. This is the easiest and the fastest way. Unfortunately, it is often not successful.
- Contact the app store with an official application and documentary evidence. You can do this by following the links: Apple App Store, Google Play Store, Microsoft Windows.
- Send a notice to the Digital Millennium Copyright Act (DMCA) US only.
- Make this cloning and theft publicly known. Gather documentary evidence and disseminate information about the cloning through blogs, forums, and social networks. It is also suitable to review the app clone and state the nature of this product for their potential users to see.
- Use a patent attorney or lawyer. This is the most expensive and long way; but if you win, you will not only get rid of your competitor and secure justice, you will also receive damages.
Take care of your ideas and products and appreciate your time. Cooperate only with reliable partners and providers.
Good luck with your project!
 Services
Services
 Work
Work
 Company
Company
 Blog
Blog
 Contact
Contact